Many non-technical folks in the U.S. first heard of encryption during the Edward Snowden leaks. When sharing secrets or private information encryption can come in handy but isn’t only used by whistleblowers, government spies, or criminals. In fact, it’s used every day in the background of many sites that handle your most precious information and the technical tools are available to everyone who wants to keep their data from prying eyes.
History Of Encryption
For as long as humans have existed there has been a desire for privacy in our communications. While cryptography is a relatively new science in the grand scheme of things, creating ways to obscure private correspondence dates back to Ancient Egypt if not before that. Coded inscriptions of hieroglyphics were featured in the tomb of the nobleman Khnumhotep II, who lived around 1500 BCE.
Egyptian hieroglyphs were some of the earliest discovered uses of encryption
Various communities, governments, and organizations have used methods to obscure their communications. Julius Caesar is another early user of encryption — he created a secret way to communicate with his generals that relied on ciphers which are like a key that unlocks the meaning of a secret phrase. If you know the way in which something was encrypted then you can decrypt it to reveal its contents.
Why Use Encryption
Some people may be familiar with writing notes to each other in grade school that switched some letters for others in messages that outwardly look like gibberish. Encryption is basically that but on a higher level of complexity. There are many different kinds which I’ll get into later but as computing has gotten more advanced so have the ways we hide data from snoops.
You may be wondering why you need encryption — you’re not a government agency hiding military secrets so why bother? As I’ve written before, while many people don’t care about privacy initially they certainly do when it’s their private messages, pictures, videos, browsing history, etc. that gets shared for the world to see. You don’t have to wait until it’s too late and there are varying degrees of encryption you can use to protect yourself.
The threats to your data are numerous and not just targeted by rogue hackers — often governments and corporations collect your data for numerous reasons ranging from the nefarious to the absurd or just the advantageous.
You can encrypt your browser, the data on your computer, your emails, your private messages, your mobile phone — all the things! As complex as encryption is, the tools are getting much easier to use and are imperative in the age where data is more valuable than ever.
Will encryption protect against everything? No. But it is an extremely useful tool to provide you with more peace of mind regarding your most precious data.
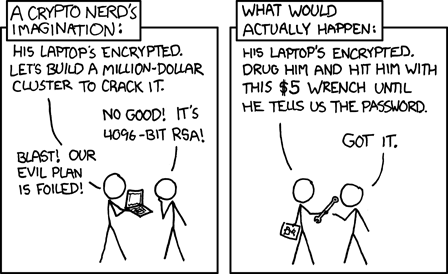
The dreaded wrench attack is an older but still effective attack vector.
Not All Encryption is Created Equal
When I talk of scrambling information so only intended parties can read them, there are a few different ways to do this and they all have their pros and cons. Each way you can encrypt and decrypt data will usually fall along these types of encryption.
Asymmetric Encryption
Though the first implementations of asymmetric key encryption were created in the early 1970’s, the work of the cryptographers who invented it wasn’t declassified until 1997 because British government intelligence is serious business. Asymmetric encryption is also known as public key cryptography. With asymmetric encryption, a unique key pair is generated for each user with a private key and a public key and the public key can be shared with others while the security of the private key must be kept, well, private. For example in an email exchange, data is encrypted with the public key of the recipient that was shared with the sender and then the recipient uses their own private key to decrypt it.
Highly complex math makes it to where you can’t determine what the private key is from knowing the public key. A common analogy is a locked mailbox slot where data or mail can be added to the box by anyone but only the person with the key can unlock it and gain access to the mail. If this private key is compromised by being stolen or shared with others, your mail or data can be stolen. An advantage of this type of encryption is that only one user has access to the decryption key and they are solely responsible for securing it.
A cool feature of asymmetric encryption is digital signatures which allow you to generate a signature from your private key that can be verified with your public key. This is a way to verify that the person who signed a message is also the same person sharing the public key. It also can aid in verifying the identity of someone sending data through insecure channels. You see this encryption used in software updates where developers sign updates with their digital signature and because it can be matched with their public key you know that the update is valid and not malicious. Sites that use HTTPS also generate certificates using this type of encryption to secure your communications. Another way public key cryptography is used is for shorter messages that communicate the exchange of symmetric keys. RSA was one of the earliest forms of asymmetric encryption and combines digital signatures with secure key distribution.
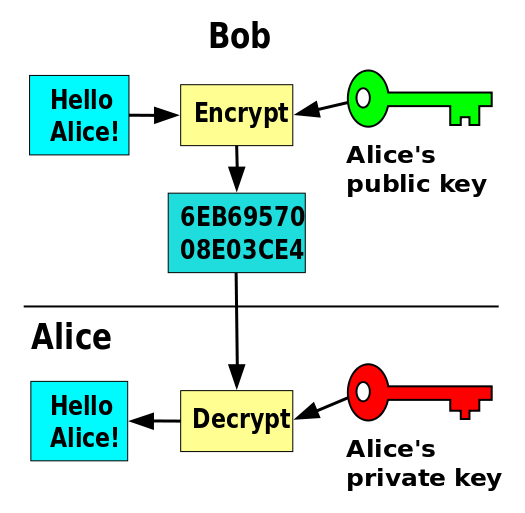
A simple break down of asymmetric key encryption.
So what is a potential issue with asymmetric encryption? Well, it is susceptible to man-in-the-middle attacks (MITM). This type of attack is when an outside party tricks the recipient of the public key into thinking that the public key sent to them is authentic when in fact it is not. One way to safeguard against this is by using a trusted third party like the Web of Trust to authenticate that the public key sent to you by someone else matches the public key that belongs to them. And since the integrity of your encrypted data depends solely on your protection of your private key, you always want to make sure to properly secure your private key. Asymmetric encryption also takes up more computing power and can be slower to decrypt data so oftentimes you see it combined with forms of symmetric encryption,
Symmetric Key Encryption
In contrast with asymmetric encryption, symmetric encryption is a type that uses the same key to decrypt data. So, instead of two parties having different keys, they both need access to the same one to properly reveal the data being transferred. Some ways you see symmetric encryption used is in cloud storage, disk encryption, and Off-The-Record messaging. The biggest downside to symmetric key encryption is ensuring that both parties are properly securing the decryption key and that only intended parties have access to it. Access to this decryption key is accomplished by both parties sharing a secret like the correct password or passphrase. The Data Encryption Standard (DES) was at one time the most widely used symmetric key algorithm but it has since been replaced by the Advanced Encryption Standard (AES).
Symmetric key encryption is better for encrypting longer messages. The encryption program Pretty Good Privacy (PGP) combines asymmetric encryption with symmetric encryption where the former is used to securely send the public key and the latter used to scramble the longer message.
Hashing
While technically not a form of encryption, hashing uses similar techniques to translate data into something indecipherable unless correct data is entered to match it. Hashing is how passwords are stored encrypted. When you store passwords on a server, that server can be vulnerable to attack and if compromised will threaten the security of likely several sites a user visits since password reuse is still common. In the event of a breach of a server that only stores hashes, however, the attacker receives useless information resembling gibberish similar to if someone is viewing an encrypted email before decryption.
Hashing translates the password (or other data) into a long string of numbers and letters unique to that data alone. This process creates a way to for a server to verify a correct password without storing the password itself. This string, called a hash, has three components: the same data will always create the same hash, it’s impossible to derive the original data from just viewing the hash, and the resulting hash cannot be recreated by other data. When hashes are stored rather than passwords, each time a password is entered and sent to the server, it corresponds to a very specific hash — if one unit of the password is incorrect it generates a hash so different that it is known that the password is inaccurate. The structure of a hash can not be traced back to the password it was generated from similar to how you can’t derive what a private key is from the analysis of a public key.
When creating a hash it is important to use well audited password hashing functions as weaknesses in implementation can make hashes vulnerable to brute force attacks. Brute force attacks can be used against all forms of encryption and work by expending a lot of computing power to calculate and test passwords. Longer passwords are harder to guess and add protection by increasing the energy needed to crack them which is why a main element in all forms of encryption is creating long, strong passwords.
There are several ways these three units work together and separately to keep your valuable data truly private. In the next sections, I’ll go over which devices you might want to encrypt. As always, assessing the necessity of encryption for each device is needed but if you store any financial or other sensitive data on your devices it’s highly recommended you use some form of encryption.
How To Encrypt Your Phone
The first items you’ll want to encrypt is your local data on your mobile devices and computer(s). I’ll cover mobile devices first. On Android and Apple phones, this process is pretty straightforward.
Some notes on mobile device encryption: your phone may run a little slower and it can’t be reversed. I’ve encrypted my Android devices before and did not notice a significant performance change but this can vary across devices. Encryption may not be necessary for everyone but for those who are concerned about warrantless searches, some states like California have ruled that warrants are required if devices are encrypted whereas if your phone is stolen unencrypted they do not need a warrant to go through it. Do not regard this information as legal advice. Consider the sensitivity of the data on your phone before encrypting.
If you use an iPhone simply go into Settings > General > Passcode. Follow the prompt to create a passcode (be sure to make it longer than 4 characters for security), then scroll down to the bottom of the screen and verify that “Data protection is enabled” is visible. For added protection you can set the phone to erase data after 10 passcode attempts and set passcode to ‘Immediately’. Apple has done an excellent job at making sure your encrypted data can’t be accessed by them or anyone else even if they have a warrant. On iOS 8 on iPhone 5S+, a PIN becomes a very secure method of authenticating with the device since they now utilize a hardware secure element.
On Android devices you’ll want to do some prep as the process is more time consuming. First, set a PIN or password (remember the longer the better as long as you can remember it), plug in your phone, and be prepared to leave it alone for an hour or more. You don’t want to interrupt the encryption process as some or all of your data can be lost. Under Settings, go to Security and select Encrypt. The phone will reboot a few times during the process and the encryption is irreversible. If you change your mind later you’ll have to do a factory reset.
Voilà! That’s all it takes to encrypt your phone.
How To Encrypt Your Computer
You should encrypt your personal computer if you store any valuable data on it and absolutely encrypt your work computer. PCs and Macs are even more vulnerable than mobile devices as there are more ways for hackers to attack them. Perhaps more of a concern than hackers is that we’re sometimes awful at physical security and in the event that your laptop is stolen, encryption can protect your data from common thieves.
Encryption is not a one size fits all solution for security, however, and it’s important to mention that it can’t protect against carelessness like leaving a computer unattended and unlocked or giving your password to those you think you can trust. Basic safety measures like having a timed screen lock with a very strong password are just as crucial to protect your encrypted data. Encryption will also not protect you if you send private information over other unencrypted channels like email. You’ll want to make sure those networks are also encrypted if you choose to share valuable information with others.
Different users require different levels of protection, so I’ll briefly go through a breakdown of the different ways you can encrypt your computer.
Full Disk Encryption
Full disk encryption is when the entire contents of a disk is encrypted. The disk can be decrypted during use by entering a password. Full disk encryption prevents people from accessing your data and booting up your computer unless they have a password. This is an appropriate level of encryption for most users and those that have a dedicated work computer. You must be certain to keep your data backed up and your backups encrypted. Full disk encryption is also the most secure and easy to use kind. On Macs full disk encryption is available through FileVault. Windows provides full disk encryption through BitLocker.
Single-User File Or Folder Encryption
This level of encryption may be more useful for those with specific sensitive files to encrypt after log in. With this type of encryption you can choose which specific files to encrypt and ideally only one user has the ability to decrypt the files so if your computer is left accessible to others they would still require a password to get into certain files. Some services do this by creating an encrypted, virtual drive where the files can be easily moved to and stored. Single file encryption can allow you to send encrypted files over other networks that can only be decrypted if the intended party has the key. Some examples of services that offer single-user file/folder encryption are EFS (Windows 2000 and later), Utimaco, PGP/GnuPG, Adobe Acrobat, and MS Office/OpenOffice.
Multi-User File Or Folder Encryption
Encrypting files that multiple users need access to is another possibility but more of a challenge to successfully implement. At this level the data can be protected by having multiple keys to decrypt it or multiple users having access to a password that can decrypt. This type of encryption faces some complexity in application because of multiple users having access to the data and because of this it is used less frequently than other types. Multi-user file/folder encryption can be helpful when it comes to servers being compromised or in the event someone tries to steal the data by backing it up on an external hard drive.
If you can’t decide between the three, go with full disk encryption — it’s the easiest to use and protects your files when logged out. Set a timed lock out in your settings that requires a password to get back in after a few minutes of inactivity. If you share a computer with someone else, single-user file/folder encryption can hide your more sensitive data.
How To Encrypt Your Internet Connection
In front of a web address you usually see the letters “http://” or “https://”. Hypertext Transfer Protocol or HTTP is a protocol which facilitates communication across the net. When browsing over unsecured connections it is very easy for attackers to gain access to your passwords and sensitive information. HTTPS ensures that information communicated between the client and server is encrypted and secure. It authenticates that the website you are on is the correct one and protects against certain attacks (like man-in-the-middle) which can forge credentials and trick users into thinking they are communicating with someone or a service that has been compromised. Though it had its start on websites that processed payments, now as many as 30% of the most popular websites use HTTPS. You can be sure that your connection is secure by looking at the letters before the web address at the top of your browser.

A secure connection will display a green lock in front of a green “https://”
If it only says “http” instead of “https” you are using an unencrypted connection. To make sure you always use HTTPS, you can download this handy extension called HTTPS Everywhere.
Another measure you can take to increase your privacy is using a Virtual Private Network. A VPN extends a private network across a public one like the internet. VPNs are often used in corporate environments to allow employees to access their work network from home but can be used by anyone who wants an extra layer of privacy while using the internet. VPNs are useful for protecting yourself against packet sniffers which are used to intercept and store data transmitted over networks. Attackers using packet sniffers will only see encrypted information if they try to gain access to your web traffic. They also employ authentication for users so no one else can log in and use the service and can detect if messages sent over the network have been tampered with.
There are several VPN services and PCMag did an excellent breakdown of the different kinds you can choose from in their article titled The Best VPN Services for 2015.

How VPNs obscure your web traffic to keep you anonymous.
If you’re even more privacy concerned, yet another option available for encrypting your connections is using Tor. Tor, an acronym that comes from the software known as The Onion Router, directs traffic through a decentralized network to obscure your IP address. Your IP address is what identifies your device when you connect to the internet and, if your activity is being monitored, can be traced to all your activity in the internet and your physical location. Tor takes your IP address and with some funky anonymization techniques changes it into another one — this masks your true IP address and location. Tor is the tool Edward Snowden used to obscure his location when deciding to become a whistleblower. You often hear Tor used in reference to “dark web” activity, but it is a tool used by many people who have very good reasons for staying anonymous.
How To Encrypt Messages
So you’ve gone through the trouble of encrypting your smartphone, files, and perhaps you’re using a VPN + Tor. Nice! But wait, there’s more; another crucial component in security is making sure your messages are secured which can be done for email services and other instant messaging apps.
How To Send Encrypted Email
One of the oldest standbys of encrypted messaging is the humbly named program Pretty Good Privacy (PGP). PGP is so good that Edward Snowden used it to communicate with Laura Poitras and Glenn Greenwald when he leaked documents revealing extensive NSA corruption. It is considered a standard in security spaces for encrypting your email so much so that government agencies themselves rely on it, but you don’t have to be a keeper of government secrets to use it effectively.
PGP combines hashing, symmetric key encryption, and public key encryption to create a so far uncrackable level of privacy. PGP works by generating a public-private key pair for users; the public key encrypts the message and the private key decrypts it. Highly complex mathematics makes it to where one could not derive the private key from the public key so there’s no danger of messages being revealed if one has access to your public key similar to the way public addresses work for bitcoin users. You can share the public key as an attachment in an email to let the intended party know you have the ability to communicate privately. When successfully encrypted, the body of your emails will appear as gibberish but the metadata (to and from fields and subject lines) are not encrypted.
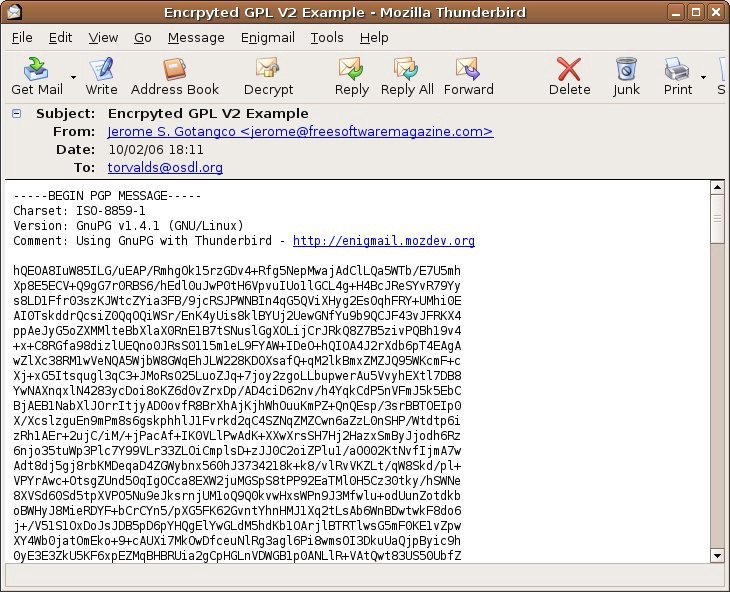
An example of what an encrypted email looks like before it is decrypted.
GnuPG offers a free version of PGP and is what Edward Snowden used. For a more thorough explanation of how to set up PGP, I recommend Chris Pacia’s article on bitcoinnotbombs.com titled Beginners’ Guide to PGP.
The process of setting up PGP can take some time and is considered pretty difficult (but not impossible) for average internet users. Admittedly, I found it challenging when I first set it up and I don’t come from a technical background. Private email providers make encrypting your emails easier and some examples include Hushmail, ProtonMail, and Riseup.net. Mailvelope works through a browser extension and OpenKeychain provides encrypted email on Android devices.
Using Encrypted Instant Messaging
You can encrypt your IMs, texts, and other real time chats with services that utilize high levels of encryption and many of these services have the added benefit of self destructing within a certain time frame. Clients that encrypt communications in real time chats are known as Off-the-Record (OTR) messaging. The main type of encryption used for OTR is symmetric key encryption. This allows two users who share a secret to access the same key to decrypt communications. An example may be asking someone where you first met to authenticate them. Also unlike PGP, OTR is much easier to use.
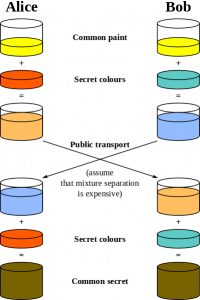
OTR uses something called the Diffie-Hellman key exchange algorithm which allows users (even ones who have never met) to exchange key information over a public network which renders them indecipherable to eavesdroppers. This is necessary as OTR messaging apps operate over insecure and monitored platforms like Facebook and Google Talk. The Diffie-Hellman exchange works a bit like the image below.
An OTR client I’ve used before is Pidgin which integrates with Facebook Messenger, IRC, AIM, Google Talk, and a host of other messengers. It’s easy to set up and a great intro to secure chatting for those new to using encryption. Pidgin is available for Windows, Linux, and other UNIX operating systems and Adium is the equivalent for Mac users. Tor Messenger also looks promising and sends all traffic through encrypted channels.
Encrypted Text Messages and Encrypted Phone Calls
Encrypted text messaging is another tool for users who are on the go and want higher levels of security. Court rulings have allowed law enforcement to gain access to your phone calls and texts through your service providers without a warrant or even probable cause. Ugh. You probably have nothing to hide but this is still a huge breach of privacy! Sensitive medical information or family issues that strangers have no business knowing are often communicated via our phone calls and texts. Thankfully, your (sometimes begrudgingly) law submitting service providers do not have access to properly encrypted communications.
There’s been a lot of debate over the security standards of encrypted text messaging apps and the levels of security depend on your personal threat assessment levels. One feature to consider would be does the app delete messages after a certain time period or store them so you can go back and reflect? Another question to ask is if the service open source? Most of us are not targeted by government agencies so some of these concerns by the hyper-security aware don’t apply to us but make for interesting reading if you want to dive deeper.
So what are our options? For iPhone users, iMessage does a decent job at keeping your communications private and Signal allows you to send private messages from iPhone users to Android users. For Android users, TextSecure is great and allows you to message anyone in your contact list (with encrypted chats occurring only with users also using TextSecure) and Knox for Samsung is protected by a hardware chip model that keeps your texts secure in a physical chip separate from the rest of the phone. Telegram is also a popular cross platform app that boasted a high bounty for hackers clever enough to find weaknesses.
I’ve personally tried TextSecure and Telegram and found them very intuitive to use. Keep in mind that with some of these apps you have to initiate the secret chat in the settings as it is not always the default. Many of these apps also offer a cool self destruct option for enhanced privacy. That’s right — you can have James Bond level tech right in your pocket. And even if you’re not a spy, using encryption for even mundane communications drives development of this form of defensive tech.
Want to encrypt your phone calls? Signal, RedPhone, and Textsecure also allow you make encrypted phone calls. Open Whisper Systems is the group behind all three of these apps and they are all cross compatible between devices which means you can call and text between iPhones and Androids securely. It’s also telling that Laura Poitras, Edward Snowden, and Bruce Schneier all encourage the use of Open Whisper Systems apps.
The Edge Security Solution
Our app takes a different approach to security where we focus on the end devices rather than securing servers and any data that is communicated to our servers is in encrypted form. This is called Edge Security. Your bitcoin data is stored locally encrypted on your phone, and independent of your device level encryption. In addition, the high level security is built into the app which will automatically backup and synchronize your encrypted data across several devices. You don’t have to utilize encryption or synchronization on the device to be able to experience encryption — it’s built right in. So, even if your phone is not encrypted, your money is. We think this is the future of encryption and makes high standards of security more accessible for everyone.
Information Security Resources
Encryption is a deep subject and this article only scratched the surface. If you’d like to dig deeper in learning about encryption there are several great resources out there to expand your knowledge. I recommend some of these sites:
Electronic Frontier Foundation
Chris Pacia’s (of OpenBazaar) security series on Bitcoin Not Bombs
Brian Sovryn of Sovryn Tech’s blog and podcast
Keep calm, and encrypt all the things!