The privacy focused cryptocurrency, Monero, underwent a successful hard fork on November 30th. Congratulations to the Monero community and the developers that worked hard on this upgrade.
Hard-forks of cryptocurrency networks require everyone on the network to upgrade their software in order to stay compatible with the majority of the network. This means Monero miners, nodes, and wallet operators cannot run old versions of the Monero protocol because these versions will be incompatible with the current upgrade.
There are four changes to the protocol in the latest version of Monero, one of which is extremely significant.
Minor Changes:
- Transactions now require at least two outputs to be considered valid. Cryptocurrencies like Monero use the terms inputs and outputs to describe the source (input) and destination (output) of funds. The new rule means Monero transactions are required to have at least two destinations for every transaction. This requirement increases privacy on transactions that would have had only one destination associated with them, making it easier to tell which address was the recipient of funds. When there are 2 outputs its harder to tell which destination is the recipient of funds compared to a transaction that only has 1 output.
- Most Monero wallets, by default, require funds to have at least 10 confirmations to be spent. This default could be changed by anyone who wants to remove that rule in their wallet software, but that won’t be the case after the upgrade. Going forward the protocol itself will enforce the 10 confirmation requirement, not the wallet software. This means recipients of Monero will have to wait about 20 minutes to spend any funds sent to them. Senders will also have to wait about 20 minutes to spend any change associated with transactions they’ve made.
- Long payment IDs have been removed from the protocol. Payment IDs were used to identify specific transactions, but have proven to be more troublesome than the protocol developers imagined. They’ve caused services and users some headaches. Users often forget to attach Payment IDs with their transactions, leading services to search for and figure out whose transaction is whose. In addition, services can’t batch multiple payments because Monero transactions are limited to one Payment ID per transaction. Batching payments allows users and services to send multiple payments to different people/entities with only one transaction. Going forward, Monero users will be able to match incoming transactions from a particular sender and batch payments with the use of sub-addresses. In Monero wallets users can create different accounts that each have different addresses. Within those accounts users can create more addresses called sub-addresses. Sub-addresses allow recipients of funds to create unique addresses for every potential sender of funds. This increases recipient privacy, makes it easier to identify a sender’s payment, and allows senders to send multiple payments in one transaction if they have many recipients’ sub-addresses.
Major PoW Change:
The major change to the Monero protocol is its transition to a brand new PoW algorithm built from scratch. The reason for the transition is the Monero community’s commitment to ASIC (Application Specific Integrated Circuit) resistance.
The Monero community wants to preserve their independence from the small number of ASIC manufacturers in the market and keep mining as accessible and egalitarian as possible. Preserving these qualities aids in maintaining the relative decentralization and accessibility of their network, which they value highly.
The previous proof of work (POW) algorithm, CryptoNight, kept Monero ASIC free for about 4 years, but the Monero network has since forked several times in 2018 and 2019 to kick off unwanted ASICs that were discovered dominating mining. They did this by making changes to the CryptoNight algorithm that would render the ASICs obsolete. The previous forks were successful in removing the impact of ASICs on the network, but were only successful temporarily. ASICs returned each time.
In response, the Monero community has opted to transition to a brand new PoW algorithm called Random X instead of tweaking CryptoNight again. Like most algorithms designed for ASIC resistance, Random X is memory hard, meaning the memory required to mine the coin is significantly higher than other algorithms that only require computation. Memory-hardness levels the playing field for other general purpose devices to compete against ASICs. ASICs have no material advantage in memory over general purpose hardware. Memory requirements limit the effectiveness of purely increasing the speed of computation, the key advantage of an ASIC.
In addition to memory-hardness, Random X generates random programs that are designed to use as many CPU components as possible. The goal here is to optimize the mining algorithm for CPUs to the detriment of ASICs. CPUs are very good at executing a broad range of programs, whereas ASICs are not. Developers of Random X believe its memory hardness and production of random programs will fend off ASICs for many years to come.
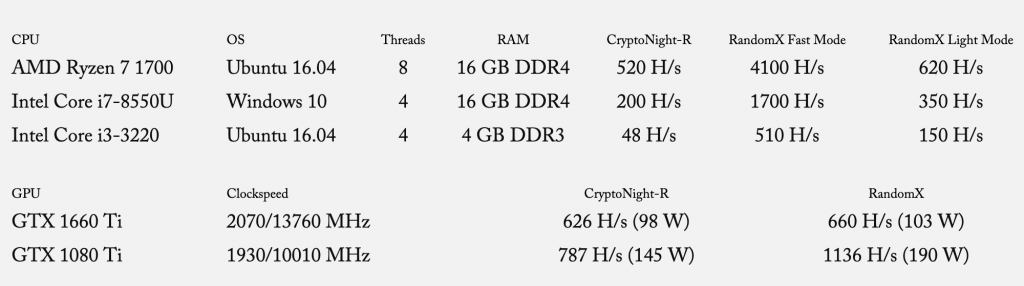
RandomX also enables CPUs to be very competitive with GPUs. Below is a chart detailing the performance of different CPUs and GPUs when mining on CryptoNightR vs mining on RandomX. The measurements show that CPUs get a huge boost in performance when switching from CryptoNightR to RandomX, while GPUs don’t see the same magnitude of improvement.
Other Points of View
Many remain skeptical of the efficacy of ASIC resistance. Although it does lower the barrier to entry compared to ASIC dominated networks, this doesn’t necessarily imply increased security. A few networks that have optimized for ASIC resistance, such as VTC, BTG, and XVG, have been successfully attacked. We have not seen this happen to networks with specialized hardware dominating mining.
Networks that favor mining with widely available hardware like CPUs and GPUs open themselves to attack from a wide range of computing power that has no connection or commitment to the network. This computing power can attack the network and then move on to other operations with little economic downside.
Networks that have specific hardware dedicated to mining, like Bitcoin, don’t have this problem. There are no computers outside of the network itself that can attack it. The attacker wouldn’t have the appropriate hardware. An outside party would have to develop or buy a lot of specific hardware to attack a network secured by ASICs. It is true, miners in this type of network can attack the network they’re mining, but they’re destroying the only use of their hardware as well as faith in a network they’ve made a considerable investment in.This would be extremely expensive and highly irrational considering there are few, if any, other uses for their equipment.
However, the hardware for ASIC secured networks is typically dominated by only a handful of hardware manufacturers due to economies of scale. This concentration of manufacturing can make many nervous about a network’s vulnerabilities and dependence on a few entities. A network dominated by general purpose hardware doesn’t have to contend with this issue.
It’s early in the history of these networks, but it looks like a multiplicity of security architectures could co-exist and provide good enough security for their respective networks. Regardless of the setup, the security architecture of all of these networks depends on the assumption that honest nodes will outnumber and outmaneuver malicious nodes. If this stays true for Monero, and they are able to adjust to threats successfully like they’ve shown the ability to do, the network has a bright future.
It’ll be interesting to see how long RandomX can fend off ASICs and what the Monero community will do to combat this ever looming threat.
Monero in Edge
Edge users and their Monero assets are safe. However, Edge users will no longer be able to send Payment IDs since it will be removed from the protocol. Our wallet never generated payment IDs, so we’ll be compatible with the upcoming deprecation. In addition, we’ve always supported sub-addresses and will continue to do so.
If you have any questions or issues don’t hesitate to reach out to our support team at support@edge.app.